-
Private Service by Phone
Within the
US or Canada 888-590-0250
Global
+1-571-405-5591
Within Switzerland
0800-564-372
Compartmentalized Routing
If You Have a
Personal ContactMost calls are automatically routed,
Otherwise, if you maintain good infosec by obfuscating your caller data, and
based on your caller metadata.
if you are presented with the automated menu,
please enter your contact's extension, or please press 2.If You Do Not yet Have a
Personal ContactPlease press 2 for the Dignitary Discretion division.
Established Clients
Dignitary-Style Compartmentalization
Your concierge is your primary point of contact regardless of the topic.

Most calls are automatically routed, but
if you are asked to self-identify,
please do not disconnect after announcing yourself.
Call announcements are not saved.Welcoming Your Call 24/365
Foremost a Professional-Services Firm
Secure Calls and Voice Mail
Routine messages are encrypted with variable-location obfuscation. Restrictive access is safeguarded with counter-ACINT audio.
During live calls and voicemail messages, you are welcome to identify yourself by cryptonym or other reference.
If you are an established client, and if you leave a voicemail message, you are welcome to request any encrypted-call protocols, encrypted E-mail methods, and/or timing preferences.Considering our specialized services with intensive client complexities, and because we do not use the pools of operators and clerks that are customary of high-volume consumer services, calls occasionally cannot be immediately answered.
In the event that you are routed to voicemail, please indeed leave a detailed voicemail message. Every message is handled securely and carefully.
Concierges and other professional-level members of your dedicated team receive messages day and night, 365 days.
The restricted accessibility of messages is an example of the slower inconveniences of security,
but preventing porousness is a primary objective. - Private Service via E-mail Every E-mail from a current or prospective client is carefully handled.
- Confidentially Routed
- Protective of Your Secrecy Compartmentalized • Advanced Multi-Layered Security
- Private Service Resourcefully Custom Arrangements Prompt, Personal Responses to Detailed Inquiries
-
Welcoming Your Preferred Protocols for
We offer you respectful control of sensitive interactions.
We welcome your preferred protocols for encrypted and physically present communications. With Regularly Priced Services that are Directly Reserved
We endeavor to accommodate cutouts and/or salted circuitousness for in-person preparatory meetings (within legal parameters). Unlike a customary hotelier or professional-services firm, your concierge would not become impatient or confused upon recognizing that some specifications of your protocols are merely added salt. Professional time, travel expenses, and other reimbursements would be charged for voluntarily in-person meetings that are in preparation of forthcoming services. Relevant professional rates are fixed hourly rates, generally at four hundred dollars per hour for this context.
The actual costs of related expenses are reimbursable, and fees for professional time shall apply, except as explicitly agreed otherwise in writing.
Almost anything that is lawful for unrestricted possession in the US can be accommodated, excluding whatever we deem to be compromising to security. Particularly for new clients, unless there is US federal coordination, technology is generally limited to equipment that is commercially prepackaged. With new clients, communications regarding forthcoming or prospective services are normally limited to remote voice and data, via technology that is commercially available. The following are excluded, although we would be happy to cooperate you with enabling powerfully secure alternatives:
- any protocols or technologies for which there is an uncertainty of potentially sustaining a wormhole or other security compromise;
- anything that we believe could be unlawful, malicious, or potentially tortious;
- any in-person meetings for which there is a concern of a potential for physical risks; or
- that would directly or indirectly involve a violation of our client requirements (as summarized by clicking here).
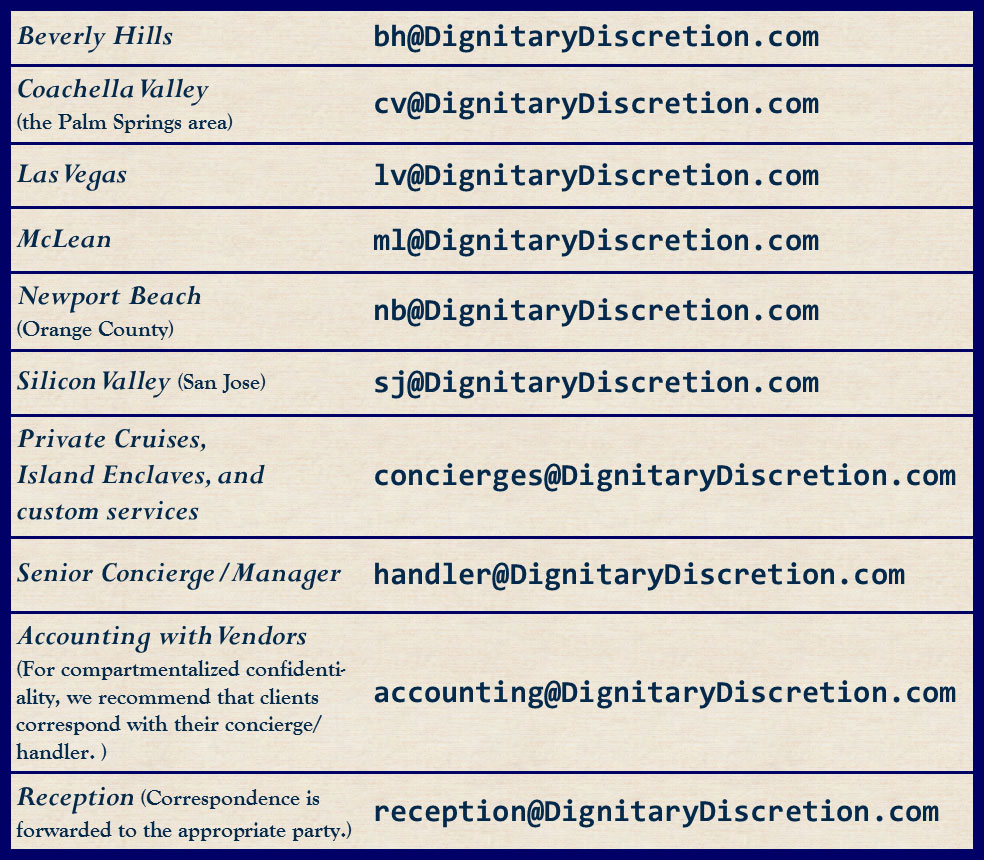
Automatically Routed Calls Securely Private E-Mail
